School ransomware attacks are on the rise—learn how to avoid becoming a victim
School ransomware attacks have been haunting district IT teams for years. One of the more recent attacks hit the public school system in Yazoo County, Mississippi. They paid a cybersecurity firm $300,000 to restore the data that had been encrypted. That payment represents 1.5% of the district’s entire annual budget.
As if that isn’t bad enough, school ransomware attacks are evolving. Some school ransomware attackers demand a payment to release access to school data. However, many attackers are using the strategy of stealing data first, then demanding payment to not only access the data but to prevent it from being released. It’s a student safety and data privacy nightmare for those responsible for K-12 cybersecurity.
Given the way that schools are affected by ransomware attacks, it’s an important issue to address. And, there are ways to make the possibility of a school ransomware attack less likely.
What is the Impact of a Ransomware Attack on Schools?
A ransomware attack late last year on the Hartford Public Schools in Connecticut caused them to delay reopening. Not all attacks have the effect of closing schools, but there are repercussions in many different areas.
![[FREE WEBINAR] How To Protect Your District's Data From Ransomware and Phishing >>](https://no-cache.hubspot.com/cta/default/6834707/8bcda64c-c821-493a-8c57-57da1e4d36fd.png)
Learning Disruption
Even when a school doesn’t need to shut down, there can still be disruptions in the classroom, especially since so many schools are still using remote learning.
For example, a ransom attack made it virtually impossible for remote learning to take place at the Huntsville City Schools in Alabama late last year. While the students who had chosen in-person classes were in session after a week, the students who had chosen the district’s remote learning option were cut off from the classroom for weeks.
Cost to Taxpayers
In monetary terms, districts that experience a ransomware attack usually end up spending a significant amount of money to fix the problems caused. Whether they pay off the criminals or pay for outside assistance, the costs can be debilitating.
Schools are funded in large part by taxpayers in the district and, eventually, those costs to respond to an attack will be passed on to the district’s taxpayers.
Data Privacy Threats and Identify Theft
As reported by the K-12 Cybersecurity Resource Center, seven districts were attacked by cybercriminals who stole sensitive data before making a ransomware demand.
As a result, the personal information of over 600,000 students and staff members were exposed. The hackers effectively had an open invitation to successfully steal the identities of adults and children. It’s worth noting that student data privacy is impossible in these situations.
Student Safety Threats
Student cyber safety solutions are available today. They’re important because once hackers have gained access to sensitive student data such as addresses and phone numbers, some of them have actually threatened to physically harm the students and their families unless their demands were met.
![[FREE WEBINAR] How To Protect Your District's Data From Ransomware and Phishing >>](https://no-cache.hubspot.com/cta/default/6834707/8bcda64c-c821-493a-8c57-57da1e4d36fd.png)
School Ransomware Mitigation Advice
The Cybersecurity & Infrastructure Security Agency (CISA) of the federal government published a report that identifies a variety of things that districts can do to mitigate school ransomware attacks.
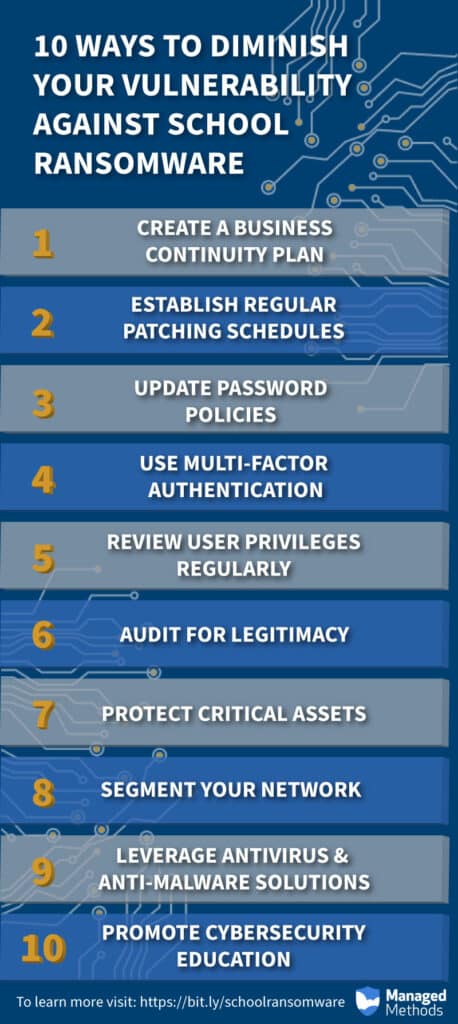
Here are the top ten:
- Create and maintain a business continuity plan. This type of plan identifies how a district will continue its essential functions in the event of a systems disruption such as a ransomware attack.
- Establish regular patching schedules. It’s critical to patch operating systems, software, and firmware as soon as those patches are available. Keeping these systems up to date will ensure that you have the latest security updates in place.
- Update password policies. Make sure that passwords to network systems and accounts are changed on a regular schedule. Also, require that users set unique passwords for each of their accounts.
- Find opportunities to use multi-factor authentication. Wherever possible, institute the requirement for multi-factor authentication by all users.
- Review user privileges regularly. Establish an audit process designed to ensure that accounts with administrative privileges are still valid. Eliminate any unused accounts and set access for all accounts using a “least privilege possible” approach.
- Audit for legitimacy. Review audit logs to ensure that new accounts are legitimate. Monitor other behaviors such as login location and traffic levels to spot irregularities that could indicate an account takeover has occurred and/or a ransomware attack is imminent.
- Protect critical assets. Identify critical assets such as student databases and remote learning infrastructures, and then backup these systems in a location that isn’t connected to your network.
- Segment your network. For example, sensitive data shouldn’t be stored on the same server and network segment as your email.
- Leverage antivirus and anti-malware solutions. Ensure that your solutions update automatically and conduct regularly scheduled scans.
- Promote cybersecurity education. Incorporate cybersecurity education in your schools’ curriculum and conduct cybersecurity awareness training for staff and faculty.
There are many myths surrounding cybersecurity. But the facts show that attacks against school systems are getting more frequent and more devastating. If you want to improve your ability to ward off cyberattacks, the NIST Cybersecurity Framework is something you can use.
Many districts have found that a K-12 NIST cybersecurity framework is useful to ensure the safety of their students and their data. Districts don’t typically have the time or funds to develop their own approach, but the NIST framework is exceptionally adaptable and scalable, which makes it perfect for school districts.

