Account Takeover Prevention
Google Workspace & Microsoft 365 Account Takeover Prevention for School Districts
Protect your district’s user accounts from account takeovers
Cyber safety and security for K-12 Schools
Detect Google Workspace & Microsoft 365 Account Takeovers
A cloud account takeover has the potential to do a lot of damage in a school district. When a criminal gains access to an internal account, it makes their activity look like legitimate, authorized behavior to traditional, perimeter-based cybersecurity tools. The result is unfettered access to all the data, files, and email addresses that account has access to.
The hacker can then upload malware into your system, send phishing emails to other contacts to gain control of more accounts, grant OAuth access to malicious apps, and more. These types of attacks are notoriously difficult to detect, and are proving costly for school districts. Using account takeover and phishing attacks, criminals have been able to divert district payments meant for vendors to their own bank accounts. They have also gained access to student social security numbers, staff W2s, and much more.
Prevent Account Takeovers
Phishing and malware attacks can lead to account takeover of your district’s Google Workspace and/or Microsoft 365 accounts. An account takeover is notoriously difficult to detect in cloud applications and can lead to additional cyber risks and data exposure.
- Protect district Google Workspace and Microsoft 365 from an account takeover with advanced phishing and malware threat protection build for the cloud
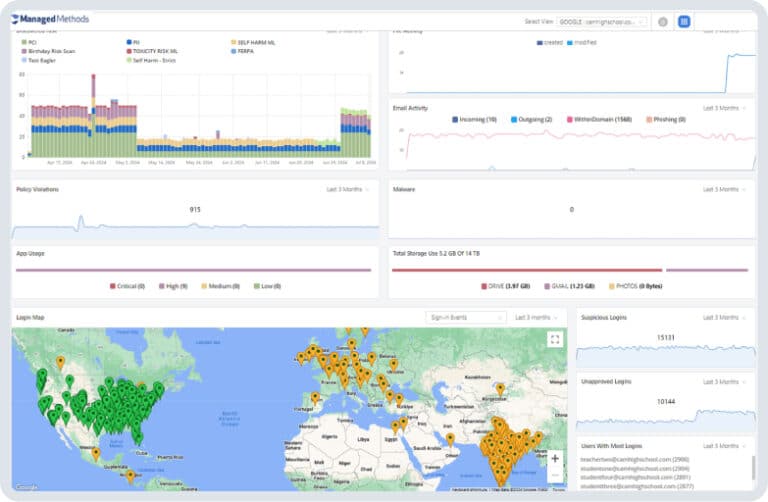
- Easily detect behavior that indicates an account takeover attack is underway, such as multiple unsuccessful logins, logins from foreign locations, and failed multifactor authentication checks
- Automatically detect and remediate successful account takeovers using highly customizable policy enforcements
Phishing & Malware Threat Protection
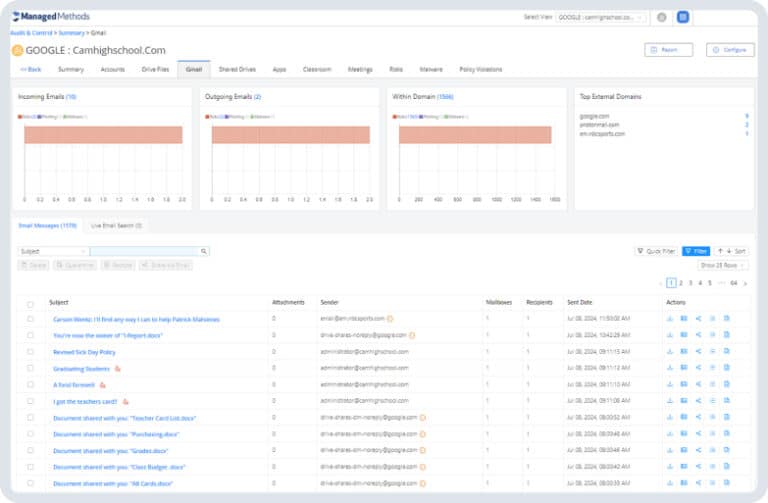
Phishing is still the #1 threat vector used by criminals to gain access to school user accounts. At the same time, schools are experiencing a sharp increase in malware—including ransomware—attacks. If your district uses Google Workspace and/or Microsoft 365, external threats can gain access to student and staff information through email, file sharing, and risky 3rd party SaaS apps.
- Scan internal & external emails for phishing and malware threats in the message body, attachments, and links
- Automatically quarantine or delete phishing emails and files containing malware
- Identify risky 3rd party SaaS applications connected to district Google and Microsoft accounts through OAuth
Protect Personally Identifiable Information
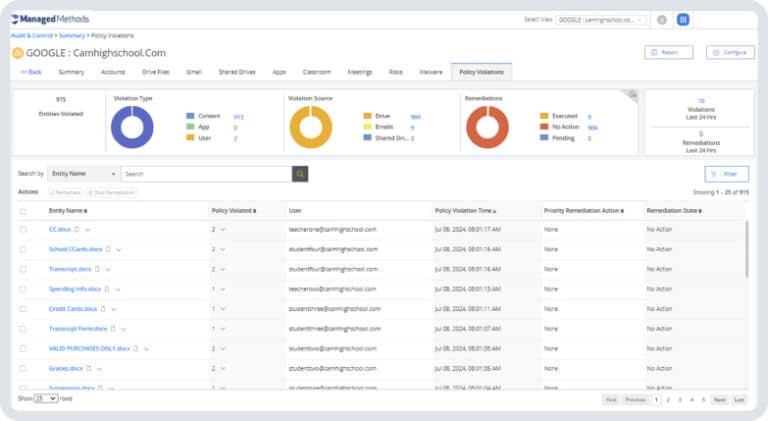
Student and staff information stored in school information systems are lucrative targets for cybercriminals. At the same time, the most common cause of school data incidents is simple accidental exposure. District IT teams must be able to manage access to sensitive information stored in Google Workspace and Microsoft 365 not only to comply with state and federal regulations, but also to protect students and staff.
- Automate data loss prevention to protect social security numbers, W2s, payment and health information, and more
- Detect anomalous events that indicate unauthorized access to data
- Identify when data is being improperly emailed or shared
- Continuously monitor behavior in Google Workspace and Microsoft 365 and automatically mitigate data security risks
Gadsden County Public Schools Case Study
“Cloud Monitor caught a dozen phishing attempts and disabled a couple of accounts that had logged in from overseas just this morning. I’m grateful that I have it to catch and remediate these attacks quickly. The Login Analyzer is particularly helpful because we’re able to see where logins are coming from. There’s no way our small team could stay on top of it all while also supporting our students, faculty, and staff.”
Committed to Student Data Privacy








Our clients






















































Testimonials
What our customers are saying
“When I first learned about ManagedMethods I was skeptical that such an inexpensive solution would be able to secure our Google Workspace data better than Cloudlock. However, after our first week using the solution, I was more than convinced. Cloud Monitor has been one of the best technology decisions I’ve made this year.”
Ed Newman
CSO & Director of Technology Services ESC 12, TX
“The addition of Cloud Monitor to our IT infrastructure allows me and my team to feel confident about protecting our students and staff when using Google Workspace. The dashboard and alerts provide me real-time info so that I can take immediate action to thwart any threats.”
Steve Bartlett
Technology Director, Bremerton School District
“Cloud Monitor provided us with a level of visibility we needed to ensure the security and safety of our students and staff. The solution was quick to deploy and gave us immediate insights.”
Tim Miles
Director of Technology, Steamboat Springs School District
Use Cases
Discover more our use cases
Cyberbullying Monitoring
Detect and respond to distress signals among students with early intervention by monitoring activity in Google Workspace and Microsoft 365.
Phishing & Malware Protection
Secure your school from phishing attacks and malware threats with proactive monitoring and threat detection capabilities.
Data Security
Ensure the safety of sensitive information stored in cloud applications with ManagedMethods' robust data security solutions.
Get in touch
Secure Your District from Cyber Threats with ManagedMethods
ManagedMethods offers advanced threat protection for Google Workspace and Microsoft 365. Ensure the security of your cloud accounts and safeguard your students and staff.