Internet Safety for Students
Our comprehensive cybersecurity products and services are designed to provide robust protection without requiring complex setup or extensive training.
Our cybersecurity products
Simplifying cybersecurity and safety for K-12 technology teams
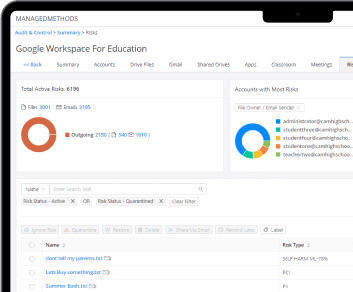
Cloud Monitor
Cloud Monitor makes Google Workspace and Microsoft 365 cloud security and safety easy for K-12 schools – no proxy, no agent, no extension, and no special training required.
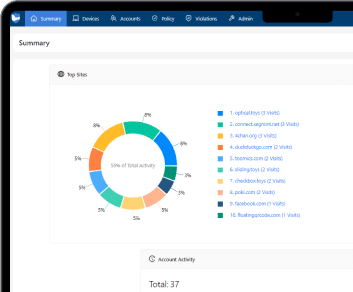
Content Filter
Content Filter is a cloud-based web filtering platform that uses browser-level URL blocking and artificial intelligence to provide internet student safety, security, and CIPA compliance.
Automate and protect with precision
Your problems, our solutions
Automate Google/Microsoft Security & Safety
Automate and optimize your Google Workspace and Microsoft 365 security protocols.
Data Loss Prevention
Protect sensitive information with automated detection and response to unauthorized access and data exposures.
Control FERPA Violations
Ensure compliance with FERPA by monitoring and managing access to student information and preventing data breaches.
Manage 3rd Party Apps
Control and monitor third-party app usage to secure your organization's data and prevent unauthorized access.
Control Compromised Accounts
Detect and mitigate compromised accounts, securing access and preventing unauthorized data breaches.
Find & Delete Specific Emails
Easily locate and delete specific emails to comply with policies and remove sensitive or harmful content.
Find Specific Files
Quickly identify and manage specific files across your organization to ensure data security and compliance.
Quarantine/Delete Phishing Emails
Automatically quarantine or delete phishing emails to protect your organization from threats and data breaches.
Manage Google Classrooms
Streamline and secure your Google Classrooms with automated management and monitoring tools.
Monitor Student Safety
Enhance student safety by monitoring digital activities and identifying potential risks or harmful behaviors.
Online Safety Alerts & Reporting
Receive real-time alerts and comprehensive reports on online safety threats to protect your organization.
Block Embedded YouTube Videos
Prevent access to inappropriate or distracting content by blocking embedded YouTube videos in your network.
Manage Lost/Stolen Chromebooks
Track, manage, and secure lost or stolen Chromebooks to protect sensitive data and prevent unauthorized access.
How it works
Dive deeper into our innovative products to understand how we make securing your digital spaces effortless and effective.
Cloud Monitor
Seamless integration
No additional browser extension, proxy, agent, gateway, or virtual appliance required.
Comprehensive visibility and control
Continuous monitoring and management across your district’s Google Workspace/Microsoft 365 domains.
Automated policy enforcement
Effortlessly implement both pre-configured and customizable policies for robust data security and student safety while you concentrate on other operational priorities.
Swift policy implementation
Lightning-fast enforcement and alerts without causing network delays, ensuring uninterrupted workflow and optimal classroom learning experiences.
Content Filter
URL filtering
Content Filter maintains a database of permitted URLs, blocking or allowing access based on predefined rules.
Blocklists and allowlists
Restrict access to blocklisted URLs and allow access to approved websites through allowlists.
Keyword filtering
The software scans web pages for specific keywords, denying access to inappropriate content.
Safety signals
Artificial intelligence inspects text inputs to detect student safety signals in real time.
Key features
Benefits you’ll love
With our cybersecurity products and solutions, your district can ensure a safe and secure online environment for your students, staff, and community.
Comprehensive Protection
Cybersecurity, safety, and content filtering provides all-around protection against online threats and inappropriate content.
Easy Integration
Integrates easily with Google Workspace and Microsoft 365, reducing setup time and complexity.
Affordable Pricing
Accessible cybersecurity and safety with pricing models that accommodate educational institutions of any size.
Real-Time Monitoring
Stay ahead of potential threats with real-time monitoring and immediate alerts, allowing for prompt intervention.
Centralized Management
Manage security protocols and configurations from a central dashboard, simplifying administrative tasks and enhancing security oversight.
Enhanced Productivity
Ensure that online resources are accessed safely and without distractions.
Testimonials
What our customers are saying
“Google Admin Console isn’t very visible or intuitive. Even when we added the security investigations tool with Google Plus edition, it’s a lot of work to dig through and find what you’re looking for. With two people here, I don't have a lot of time to spend hours looking for potential issues. Cloud Monitor automates a lot of what we would have to do manually using Google’s investigation tool. It’s a huge time saver, so if you don’t have the insight or you’re understaffed, it’s a lifesaver.”
Rich Chiuppi
Director of Technology, East Prairie School District 73
“While we have other related products, such as GoGuardian, they are very different tools that provide very different services. Cloud Monitor provides behind-the-scenes access to Google Workspace and Microsoft 365 that allows for bulk changes, automated changes, and automated flagging that are all pieces of the bigger student safety and digital safety puzzle. It's actually one of my favorite platforms to use.”
James Walker
Network System Administrator, Prince Edward County Public Schools
“In Google Admin Console, it’s tough to dig into the logins and user details to determine what’s going on with an account. Using Cloud Monitor's Login Analyzer, we can quickly see account login locations and the activity history of that account. Previously, suspicious login tracking was time-consuming. Now, we can analyze potential incidents quickly without needing to bother the end-user.
Vaughn De Fouw
Infrastructure Engineer, Kettle Moraine School District
Leaders in K-12 Data Security & Cyber Safety













Get in touch
Discover how our products can enhance digital safety for students
Explore the comprehensive capabilities of our cybersecurity products and solutions, designed to protect the digital environments of K-12 schools. Start your free trial today to see firsthand how ManagedMethods can safeguard your students and secure your district’s data.