Why you need to consider a layered approach to Microsoft cloud security
Is Microsoft cloud secure? Yes, it is. But admins really need to make sure they have Office 365 app security properly configured in order to secure their data.
When IT managers and system admins think about cloud computing, it is likely that Microsoft, Google and Amazon come top-of-mind as the go-to providers. And with Microsoft viewed as the top provider by many, it is safe to say a good chunk of organizations run on Microsoft Office 365 in the cloud.
By moving its core Office products to the cloud via Office 365, Microsoft has helped many customers make the transition to take advantage of all the benefits the cloud has to offer. Instead of company data being stored on a business device, data is stored on Microsoft servers and made accessible from anywhere via the internet.
Cloud computing allows organizations to share documents and data across many machines, and these machines running in the cloud are now everywhere. There’s a good chance the data is stored in a regional data center close to where you live and work. While this is a major benefit for organizations, it unfortunately means many organizations now have to worry about secure cloud access and the security of their data.
Is Microsoft Cloud Secure?
More often than not, we hear in the news about the latest data breach and hackers taking data of millions of people. However, most of these attacks are hitting traditional servers — not the big public clouds.
Quentin Hardy, The New York Times’ former deputy technology editor, shared a good analogy when thinking about cloud security with the big organizations, including Microsoft. “The same way that your money is probably safer mixed up with other people’s money in a bank vault than it is sitting alone in your dresser drawer, your data may actually be safer in the cloud: It’s got more protection from the bad guys.”
While this may be the case, the unfortunate reality is that there is no guarantee, and the native Office 365 cloud app security controls IT admins get with their Microsoft license is not enough to protect sensitive company data. Further, it is not Microsoft’s responsibility to ensure that you have your Office 365 apps set up properly. If you’re not using the security features offered to you, or they are not properly configured, it’s on you. Microsoft, like all cloud applications, also won’t be much help if a user account is hijacked. Once a hacker has legitimate access to an account (such as they’re able to figure out a password), the system sees that as authorized access and treats it as such. IT admins need to consider taking a layered, zero trust approach to security to provide both comprehensive and redundant protection.
Layering Microsoft Cloud Security
In cybersecurity, redundancies are necessary. IT admins should implement additional tools and protections in order to secure their organization’s environment effectively. For some, this means opting in for the Advanced Threat Protection (ATP) add-on. For others, it means heavy consideration on whether or not they need to upgrade to the expensive Office 365 E5 level to get the controls needed — even if there are a few Microsoft cloud security issues — or if a third-party Cloud Security Access Broker (CASB) is the better option.
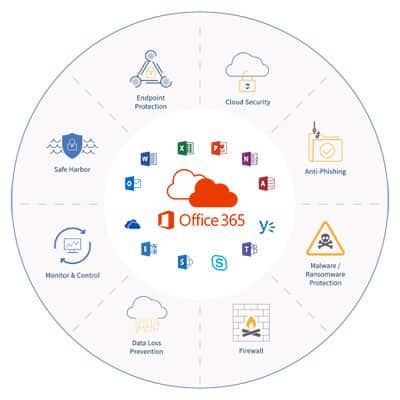
Many hacks occur not because someone broke into the cloud data center. What typically happens is that a hacker was able to exploit a vulnerability in the cloud application itself. This means a layered defense on each part of the technology in the cloud is necessary in order to get the necessary protection, which includes the following:
- Employee Education
- Network Security
- Web Security
- API-Based Content Filters
- API-Based Cloud Security
Now, let’s take a deeper dive into Microsoft’s cloud security product offerings.
Microsoft Azure Cloud Security Products
- Security Center: Unify security management and enable advanced threat protection for workloads in the cloud and on-premise.
- Key Vault: Safeguard cryptographic keys and other secrets used by cloud apps and services.
- DDoS Protection: Protect your Azure resources from denial of service threats.
- Azure Information Protection: Control and help secure email, documents, and sensitive data that you share outside your company.
- Application Gateway: Protect your applications from common web vulnerabilities and exploits with a built-in web application firewall.
- Cloud Application Security: Provides visibility, control over data travel, and analytics to identify and combat cyberthreats across all Microsoft cloud services.
[FREE GUIDE] Microsoft Office 365 Security Comparison Guide >>
Cloud Application Security Use Cases
For those looking to make the expensive jump to Microsoft Office 365 E5, a third-party CASB application such as ManagedMethods provides the effective redundancy needed. In the event a component of your system fails, a backup process is in place and you won’t lose your data — and a third-party CASB is a much lower cost toward your bottom line.
Let’s take a look at how a third-party app protects your environment on top of Microsoft’s native offering.
Data Security
When organizations move from traditional, software-based Office to cloud-based Office 365, many IT admins don’t realize they have lost critical visibility and control functionality. With a third-party solution, organizations can close the data security gap Office 365 created by:
- Securing sensitive data in-transit and at-rest
- Identifying and fixing data security risks in Office 365, as well as other SaaS applications
- Identifying the source and impact of data breaches
Threat Protection
Malware and phishing threats don’t only attack your organization through email. A threat protection solution must be able to control threats in OneDrive and SharePoint as well — a feature only offered in Microsoft’s E3 and E5 offerings. A third-party application protects your entire Office 365 environment by:
- Stopping breach attempts in all Office 365 applications, including Outlook, OneDrive and SharePoint
- Detecting and managing unsanctioned SaaS applications with risky access permissions
- Automatically detecting risks to quarantine or delete potential threats in email, file sharing and messaging applications
Account Takeover Prevention
Account takeovers are difficult to detect and are not prevented by Microsoft’s native security features — unless your organization has E5. Third-party applications are able to detect abnormal behavior and prevent account takeovers with:
- Automatic detection of suspicious logins by location and account activity behaviors
- Monitoring of all OAuth cloud applications for risks, data breaches, inappropriate and explicit content, and more
- Automatic rules and policy enforcement for easy data loss prevention management
Monitoring & Compliance
Taking steps to comply with data security and privacy regulations keeps your organization from unnecessary risks. With a third-party application, IT admins are able to enforce consistent regulatory requirements across all cloud applications for full visibility and control over sensitive and regulated data stored in the cloud with the following:
- Quickly identify data security gaps, where they exist, what files are impacted, when and how data was accessed, and more
- Easy, automated reporting for required compliance auditing
- Easy visibility into effected accounts and files with simple incident reporting
Yes, Microsoft cloud is secure. But, if your organization is using Microsoft Office 365, then you need a Microsoft cloud access security CASB solution to better secure your cloud environment. While Microsoft does provide some native security and compliance features, many IT admins are looking to third-party cloud security solutions to protect their Office 365 environment and other SaaS applications, and avoid paying for add-ons or an upgrade to the E5 level.
Is ManagedMethods right for you? Download our Office 365 Comparative Overview and see for yourself!

