11 Ways To Solve School Privacy Issues In Your District
Whether you’re a school official, teacher, staff member, parent, or even a student, protecting data privacy is a constant challenge. In the United States, where student privacy is regulated by federal law, it’s especially important for the K-12 school system to have concrete data security and privacy policies in place.
Unfortunately, privacy protection isn’t that simple. Many school districts still run into privacy issues on a regular basis, especially when it comes to cloud-based edtech tools.
Plugging the gaps in your policy is hard if you don’t know where they’re coming from. Here, we’ll discuss common school privacy issues and share 11 tips you can use to address them.
Why your district might have a privacy problem
Student data privacy is among the most significant technology debates in the U.S. school system. In fact, according to a recent CoSN survey of school district IT leaders, data privacy is the education industry’s second biggest priority behind cybersecurity.
What’s interesting is that student privacy isn’t really a recent phenomenon. Districts have been navigating school privacy issues as far back as 1974 when the Family Educational Rights and Privacy Act (FERPA) was established. However, privacy hasn’t gotten any less complicated since the creation of this watershed federal law.
In truth, it’s even more difficult today than ever before. After the turn of the 21st century, and again during the COVID-19 pandemic, school districts adopted new technologies as they evolved — and with them, a slew of privacy issues followed in their path.
External school privacy issues
Data security is an ever-present threat now that most school districts are trusting student information to digital technologies and online services. Naturally, with more sensitive data up for grabs, cybercriminals have set their eyes on the K-12 school system.
According to the K12 Security Information Exchange, 2021 was a record year for school cybercrime. Since 2016, schools are averaging more than one incident per school day. (Notably, this only accounts for incidents that have actually been reported.)
However, there’s another significant problem flying under the radar: third-party edtech providers. The vast majority of school districts operate in the cloud using applications, tools and services delivered by third-party vendors.
District administrators know that their vendors are processing, accessing and storing student information, but they might not realize many are violating student privacy in the process. Common Sense Education reports that somewhere between 58-72% of edtech apps are actively selling student records. Others may be using data for marketing and advertising purposes without parental consent.
Internal school privacy issues
What’s also important to remember is that there are internal factors that may be putting student data privacy in jeopardy. For instance, imagine what might happen if a school nurse mistakenly sends student information to the wrong person, such as a teacher or parent of a classmate.
By the same token, a school official could just as easily access and disclose an education record without parental consent. Not only are these privacy violations, but they may also embarrass and endanger the impacted student.
![[FREE] Google Workspace and/or Microsoft 365 Security Audit. Learn More & Claim >>](https://no-cache.hubspot.com/cta/default/6834707/25278544-250d-4265-b25f-0c160bf67707.png)
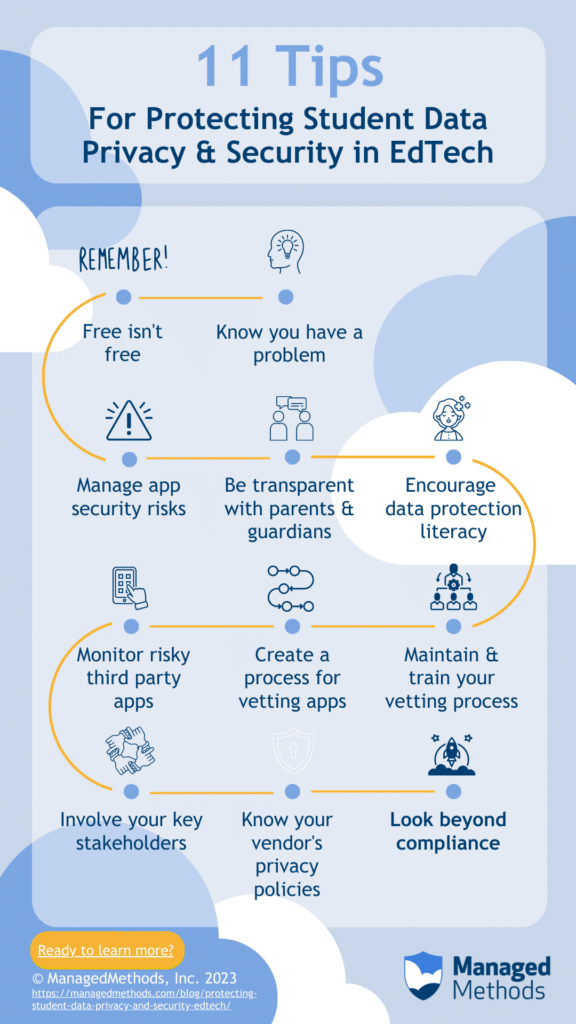
11 tips for protecting student data and maintaining privacy
We recently had the pleasure of hosting two experts in K-12 education technology and data security during a live webinar panel discussion focused on student data privacy. Our panelists — Marlo Gaddis, Chief Technology Officer at Wake County Public School System, and Libbi Garrett, Director of Resource Programs at California IT in Education (CITE) — provided valuable advice on the topic.
Here, we summarize 11 of their best tips and tricks that district administrators can use to protect student data privacy. For each one, we’ll include their key insights so you can better understand how to safeguard student information.
1. Know you have a problem
As with most challenges in life, knowing you have a problem is the first step in the right direction.
“You have to start off with, ‘Hello, my name is Marlo Gaddis and I have a problem,’” Gaddis joked during the panel discussion. “If you think you don’t have a problem, or you don’t know that you have a problem, then I hope you have really good luck. Because I’ve not met one district leader across the country that doesn’t have issues with this that they’re working through. You have to know that you have a problem and start having conversations with your leadership and others to start figuring it out.”
Believe it or not, most IT leaders don’t realize that third-party apps create risks to both data privacy and cybersecurity. Acknowledging this fact, and that it’s a problem that needs to be managed, is essential to reaching a positive resolution.
2. Remember that free isn’t free
One of the many problems IT teams are facing is the lingering presence of the many free remote learning resources that became available during the COVID shutdowns. According to Gaddis, chances are that you have a lot more apps connected to your cloud domains than you think you do.
“Free edtech tools are like free as a puppy. You know when you get a free puppy the work isn’t over. It’s just begun,” Gaddis said. “I know it’s tough because you want to use anything you can to support your kids. The problem is that there are a lot of issues with these free tools. You’re looking at manually uploading student information into a system with no privacy or security checks on the back end.”
3. Manage app cybersecurity risks
Connected cloud apps are a risk to your sensitive data whether you like it or not. There are several ways threat actors exploit third-party apps to gain access. OAuth risks, for instance, are some of the newest and most dangerous.
Using OAuth permissions granted by your users, cybercriminals can access documents and spreadsheets containing sensitive information, read, write and send emails to all contacts, and even potentially access other apps without ever logging into the user’s account.
“The FBI, CISA and MS-ISAC released a Joint Cybersecurity Advisory in late 2020, warning us that K-12 schools have the most valuable data, and yet we are the most vulnerable,” Garrett said. “And now they keep telling us and telling us. We need to take these warnings seriously.”
4. Be transparent with parents and guardians
One point that Garrett and Gaddis raised during the discussion is that parent expectations are quickly changing. While most agree that updated technology is good for learning, many still want to know how their children’s data will be handled.
“What happened is a lot more of them are now more knowledgeable about the technology we’re using,” Gaddis explained. “Now, they’re asking the questions: ‘Okay, this is what you’re using with my kids, how are you keeping them safe in this product? What are you doing with the data? What are the companies doing with the data?’ These are really great questions and they are wanting to hold us accountable. As a parent myself, I applaud them for that.”
5. Encourage data protection literacy
It takes a village to raise a child. Likewise, it takes a whole district to protect data privacy.
Nowadays, data protection isn’t merely the responsibility of your IT department. Everyone — parents, guardians, students, school staff, etc. — has a part to play. According to Garrett, it’s important for every user to understand where they fit into that process.
“We’re teaching and training our parents, teachers, and students so that they understand how to keep themselves safe in this world that is now so high-tech,” Garrett explained. “We can’t be telling people, ‘We’re doing everything right and we’re keeping you safe.’ No, we’re doing everything we can to protect them. But everyone needs to learn to see the dangers and make good decisions on their own. We need to be having those conversations.”
6. Monitor your Google and/or Microsoft domains for risky third-party apps
It’s one thing to say that you only allow vetted and approved apps to access data. It’s quite another to make that a reality.
This is true on a number of levels, one of which is actually controlling those apps in your domain. Some levels of Google/Microsoft licensing allows for some control over this, but they can be quite heavy-handed and sometimes downright impossible for many districts to manage. When Gaddis ran her initial audit with ManagedMethods, she was shocked by what she found.
“We had 11,374 applications that our students and staff were using,” Gaddis shared. “And it was amazing some of the things we found. We had folks using their district accounts for dating apps, travel apps, and all kinds of things that we had to say no to. We went through a process of identifying what had been vetted and approved. Everything else we shut off. It closed a big gap in our data protection process.”
![[FREE] Google Workspace and/or Microsoft 365 Security Audit. Learn More & Claim >>](https://no-cache.hubspot.com/cta/default/6834707/25278544-250d-4265-b25f-0c160bf67707.png)
7. Create a process for vetting apps
New edtech tools enter the market every day. You need an efficient process for reviewing apps you’re thinking about connecting to your domain (as well as those that already are). Gaddis and Garrett agreed you need a cross-functional team for creating that process. They recommend you include:
- Teaching staff.
- Curriculum staff.
- Business departments.
- Possibly your superintendent and/or a school board member.
8. Maintain and train your vetting process
It’s not enough to create the system. Once it’s established, you need to document and communicate it to your stakeholders, train them on how it works and then maintain the process moving forward. Also, you should review your process periodically and adjust as additional factors come up.
“My advice is that you don’t want to just develop your plan. You’ll also want to make sure it’s trained on appropriately, and you’re following it up with good resources,” said Garrett. “Also, have conversations and training regularly with staff so you know what’s occurring in your environment and can support needs as best you can.”
9. Involve your key stakeholders
Data privacy is too big a job to do all on your own. Garrett and Gaddis recommend involving at least one representative from the following stakeholder groups:
- Academic staff.
- Student support services.
- Finance team.
- Leadership team.
- School board.
“By involving the right people in your process, you’re empowering your staff, rather than forcing them. Otherwise, they’re going to see it as you’re putting another process on top of them to hinder what they’re trying to do in the classroom, and that is the last thing we want to do,” said Garrett.
10. Know your vendors’ terms of use and privacy policies
Whether it’s a free or paid app, you need to know the vendor’s terms of use and privacy policies. Many new vendors have recently entered the edtech market. Many may not be aware of the many unique data use and compliance requirements that are standard in K-12 and/or working with minors’ information.
“We had one vendor of a very popular application change their terms this past spring to include wording that they could geo-locate our kids. We happened to catch it, though I’d say probably 99% of districts didn’t,” Gaddis recalled. “We had to have a long conversation with the company about that change and, ultimately, we made the decision to no longer allow that application.”
11. Look beyond compliance
Student data privacy laws have been around for a long time, but rarely have regulations ever held anyone accountable. District administrators and school boards have historically gotten away with letting data security slip through the cracks.
“There are no teeth in the laws,” Gaddis said. “The idea with FERPA, COPPA and CIPA, for example, is that you could lose federal funding if you don’t follow the guidelines. But the truth is that never happens. And yet, we know that our data is more at risk.”
How to safeguard student data
Let’s be honest: Auditing and controlling applications is a contentious undertaking for most technology teams. Many continue to kick the can down the road to deal with it later. Others are ignoring it. Most simply don’t realize how big of an issue it is.
“It shouldn’t be us against our CTOs, or us against curriculum, or teachers, or superintendents or school boards,” said Libbi Garrett. “It should be all of us, nationally, against them: the people who are coming after our data.”
Fortunately, auditing your cloud domain doesn’t have to be a chore. With a cloud security platform like ManagedMethods, you can easily automate data security tasks, identify risks, and remove risky apps — all without invading student privacy. As an ethical answer to the data privacy problem, ManagedMethods is dedicated to keeping your district’s sensitive information safe.

