CASB architecture can either slow your workforce down, or secure access anywhere they go
Including a CASB is a critical component of any modern organization’s cybersecurity infrastructure. They can provide InfoSec teams with deep visibility and control over their global, mobile workforce that was never possible before. But this hasn’t always been the case. In the past, security technologies were black boxes that you placed in your data center. And, for the most part, you didn’t really look inside the security technology. These black boxes worked well in a defined perimeter, and that’s all they needed to do. But things started changing with the adoption of cloud computing technology.
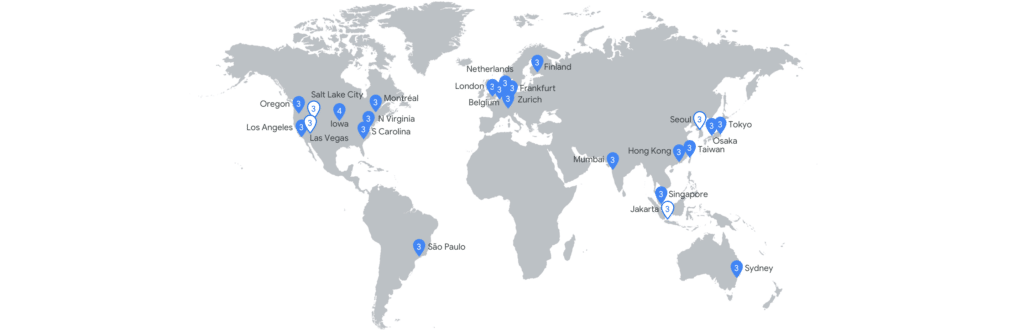
Increased adoption of SaaS applications and cloud-based email, like Gmail and Outlook 365, has improved productivity for many employees. Your end users can access these apps from anywhere in the world with very good performance, availability, scalability, and resiliency. And the infrastructure of Google and Microsoft is mind-blowing. They add more capacity on a daily basis that is larger than your entire infrastructure capacity. They are laying cables and adding data centers in every corner of the world. For example, Google is spending $13 billion on their infrastructure in 2019 in the U.S. alone.
Google Data Centers 2017
What does this mean for you and your company? You don’t have to worry much about the performance of G Suite or Office 365 (or even Dropbox and Slack, which rely on another giant in the space, AWS ). The service is always available. It is available from a location closest to your end user irrespective of where they are. It’s a wonderful world indeed.
What Does This Mean For Your CASB Architecture?

Now, let’s say you put a black box between your end users and their Gmail account. You just created a constricted pipe and made the whole user experience go downhill. It may not even be a black box, but a proxy sitting in a specific data center somewhere in Northern California. In the 90s, proxies grew like weeds and caused proxy fatigue for IT security. Now, these proxies are even worse in that they do not scale to the needs of your global and mobile workforce. A proxy between your end users and cloud apps can often be the weakest link in the chain.
What good is adopting a cloud app that’s scalable and available if you constrain it with CASB security technology from the 90s? It’s both self-defeating and error-prone.
Today, IT security teams are moving to modern cloud app security technology that doesn’t rely on proxies, agents, or any other “broker” to secure data stored in cloud applications. CASB solutions that are cloud-native provide better monitoring, visibility, and control over data in cloud apps. They also don’t impact your end users’ experiences by slowing down access to the applications they need to do their jobs effectively.
So, does CASB matter? The answer is YES!
You need cloud-native CASB architecture that is deployed on the same infrastructure as your cloud app provider. You don’t want something between your end user and a cloud app. You want a solution that uses APIs to works with your cloud app to enforce your security policy.
For a true cloud-native security solution to protect the data in and access to your cloud apps and cloud-based emails, check out ManagedMethods today!

