Data privacy and data breaches are inextricably linked
Data Privacy Month is kicking off and it’s a big, broad topic for schools this year.
The past 20 months or so have highlighted trials and triumphs in K-12. First came the monumental shift to remote learning. Followed in quick succession by “zoombombing”, school ransomware attacks (leading to data breaches of untold amounts of private and financial data), and media attention on student surveillance.
There was also positive legislative action to celebrate, including the CARES Act, ESSER funding, and the October passage of the K-12 Cybersecurity Act.
In the back quarter of 2021, ManagedMethods published a survey report in collaboration with EdWeek Research Center. To produce it, EdWeek surveyed hundreds of district technology leaders and tech purchase decision influencers.
We wanted to gain a better understanding of how well districts are protecting sensitive data. We thought this might be particularly interesting now, given the fast (and sometimes chaotic) transformation to cloud computing and education technology that happened over the past several months.
Since it’s the beginning of data privacy month, I figured it would be good to focus on some of the data breach and data loss prevention findings uncovered by the survey. Because data security and student data privacy are inextricably linked.
4 Truths You Need To Understand About Data Breaches & Data Privacy
What is a data breach? Data breaches take many different forms. Some are caused by simple accidental improper sharing and misconfigured security settings that can be thought of more as “data exposure”. Data breaches can also be caused by a malicious act to gain information that can be used for profit.
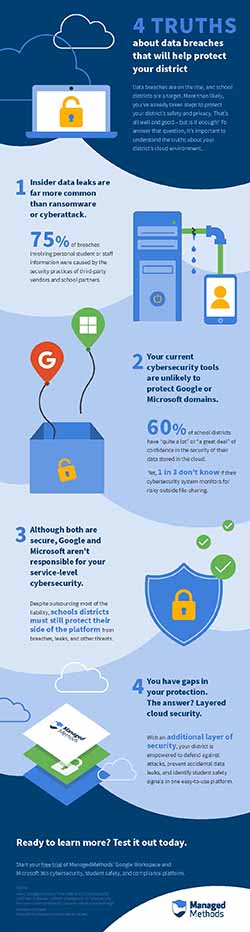
It’s important to understand these truths about data breaches in your district’s cloud environments to protect it better and help inform budget and other resources decisions.
1. “Insider” data leaks are far more common than ransomware/cyber attacks
While our survey found that tech decision-makers and influencers are more concerned about ransomware and phishing, the fear factor doesn’t quite match reality.
Reporting published by Doug Levin at K12 SIX—likely the most comprehensive and consistent reporting for K-12 cyber incidents—shows that data breaches/leaks are far more common than malicious attacks.
Now, it’s important to keep in mind that ransomware, phishing, and other types of attacks often lead to data breaches. So, the two are very closely related.
More often than not, data breaches are accidentally caused by a member of your district’s staff. Levin’s reporting also found that 3rd party vendors were the greatest contributors to school data breaches for two years in a row.
2. It’s unlikely that your current cybersecurity tools protect you from data breaches impacting your Google and/or Microsoft domains
One of the top cybersecurity myths we hear day in and day out is that schools have a firewall and content filter, therefore they’re all set.
In fact, this is likely contributing to the fact that 60% of survey respondents said they had either “quite a lot” or a “great deal” of confidence in the security of their data stored in the cloud.
Yet, nearly 1 in 3 do not know if their cybersecurity systems consistently monitor for risky file-sharing outside of their domain; and more than 25% don’t know if they can monitor data risk within their domains.
This overconfidence phenomenon is nothing new to risk management experts.
A cloud data breach is typically quite a bit different than one that impacts on-prem storage. One of the main differences is that cloud data breaches can be more difficult to detect and remediate. This is because the data lives outside of your network—in the cloud—and those in charge of district data security often have less visibility and control over cloud apps without the right tools (more on that in a moment).
The point is: Data that is stored in cloud apps—yes, that includes Google Workspace and Microsoft 365—is outside of your network. Therefore, network security technology like most firewalls and content filters cannot protect that data. And that brings us to our third truth…
3. Google and Microsoft are secure, but they’re not responsible for your service-level security configurations
This is another misunderstanding we hear all the time.
Don’t get me wrong, I’m not telling you that Google and Microsoft are fundamentally insecure or bad places to store your data. As Google for Education and Microsoft for Education Partners, we’re big believers in the power of cloud computing and the many benefits their services provide.
It’s highly likely that they’re more secure than on-prem storage in most cases. They both have the funds, global infrastructure, and expertise to build among the most secure storage centers on the planet. Simply put, they’re going to outperform your little server room when it comes to securing the storage infrastructure, platforms, and applications.
But, when you enter into a license agreement with either of them, or any cloud-based SaaS application, you’re entering into what is called a “shared responsibility model”. This means that they’re responsible for most of the data security—you’re outsourcing that responsibility from your little server room.
But you still maintain some of the responsibility for securing the service side of the platform from data breaches, leaks, account takeovers, phishing, etc. You’re responsible for making sure that access to your data is properly protected and configured.
And, yes, both do provide tools to help you monitor and maintain this. Some of these tools are provided in the free versions marketed to school districts. Others you will need to upgrade to a paid license for.
4. Your district needs layered cloud security for full-coverage security, safety, and compliance
Of course, as a third party cybersecurity and safety provider, our opinion is that an additional layer of protection is not just “nice to have” but mission critical for schools today.
Why?
We work with a lot of tech teams that upgraded to Google Workspace for Education Enterprise Edition (particularly in the past year). They understand the need for a tool like ManagedMethods for 3 reasons:
- Additional layer of security: No tool in the world is going to catch 100% of all cyber incidents 100% of the time. That’s a big part of the reason why “defense in depth” is encouraged by cybersecurity experts. And, yes, we do catch things like phishing emails, shared drive files containing malware, and suspicious logins/account activity that don’t get picked up by native Google/Microsoft tools.
- Ease of use: This can be a bit subjective, but we put a lot of effort into developing a platform that is super intuitive and easy to use. And we hear that’s true time and time again from our customers. Not to be an alarmist, but when a data breach happens time is of the essence and our philosophy is that it better be easy to find and stop any incident ASAP. Also, we know that you’re doing the work of at least 3 people over there. We strive to make tools that cut down on the amount of time needed to complete various admin tasks.
- Student safety signals: Perhaps saving the most obvious differentiator for last. We fairly quickly realized how important it is to school districts to be able to identify student safety signals in apps like Google Docs, email, chat apps, etc., and get the information to the proper student resources fast. Frankly, we didn’t initially set out to build this kind of product. But, it’s just one of many examples of how we can take customer feedback and pretty quickly turn it into usable, useful, and relevant tools in our platform.
When it comes to protecting your students’, staff, and financial information from data breaches there are no silver bullets. And technology alone won’t solve a fundamentally human problem. But it’s important for district IT leaders and those admins influencing budget and purchase decisions to understand the gaps in your cybersecurity strategy.
This report is a fantastic first step in understanding why your district may also have these gaps, perhaps self-reflect on your own overconfidence, and start taking action to create a safer space to learn and work.