Everything you need to know about mitigating your cloud computing risks with cloud application security
Most IT professionals understand the importance of securing their networks and on-prem data. And many are also beginning to understand the importance of cloud security to ensure sensitive data stored and shared in the cloud stays safe. However, there still seems to be a misunderstanding of how to secure cloud storage.
Some believe that their firewall or VPN will do the trick. Others think that they get all the security they need “out of the box” from the applications they license. And many still believe that cloud application security is the responsibility of the application vendors themselves.
Let’s take a look at what cloud application security is, what it means for your organization, and where the responsibility of securing applications, and the data stored in them, lie.
What is Cloud Application Security?
Cloud application security is a series of defined policies, processes, controls, and technology governing all information exchanges that happen in collaborative cloud environments like Microsoft Office 365, Google G Suite, Slack, and Box (to name a few).
So, if you or your employees frequently store and share data in cloud applications like the ones listed above (or any of the tens of thousands available), it is absolutely necessary to add a cloud application “safety net” to your zero trust security infrastructure.
Top Cloud Application Security Threats
It is no secret that there are security issues in cloud computing that IT teams must be aware of. According to the 2018 Cybersecurity Insider Report, the four most common cloud application security threats that IT teams are facing include:
- Misconfiguration of application setup is the single biggest threat to cloud security because data breaches tend to happen when services are accidentally exposed to the public internet.
- Unauthorized access to a website, server, service, or other system is also an area for great concern because once they’re in, there’s no telling what unauthorized users will do to create chaos.
- Insecure APIs and interfaces present easy opportunities for attackers to breach systems because they are the only asset(s) outside of the organizational boundary with a public IP address.
- Account hijacking is feared because so much sensitive data and resources is stored and accessed on devices shared by many different users—and because keeping tabs on rogue employees is difficult.
[READ MORE] Cloud Computing Security: Secure Your Data, Not Just Your Perimeter >>
What Cloud Application Security Options Are Available?
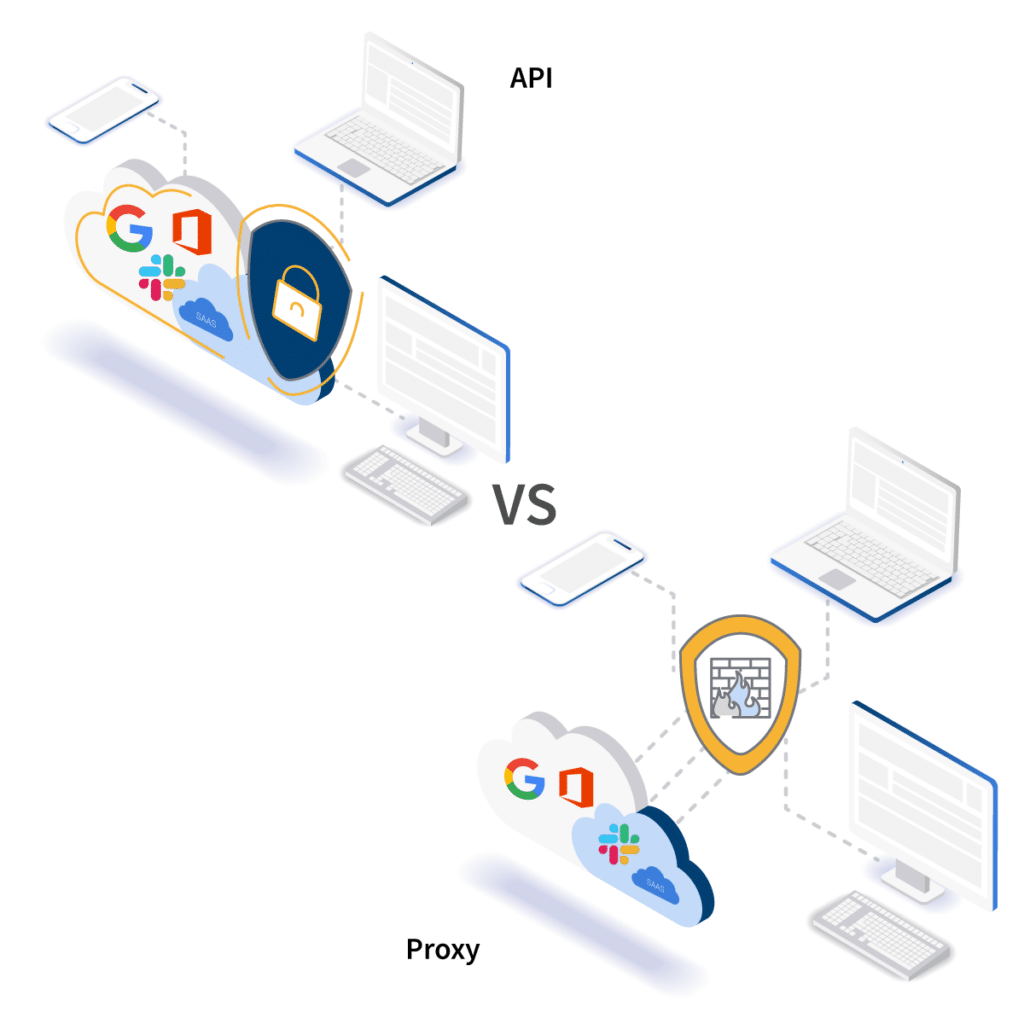
A common misconception in today’s marketplace is that you need a proxy, browser extension, or some other agent to secure cloud applications. However, there are cloud security solutions available that use the a cloud application’s native APIs to monitor, control, and secure activity within them. The two basic options on the market are between an API vs proxy CASB. API-based cloud application security platforms (CASP) are quickly becoming the favored security model for admins. This is for three main reasons.
First, a CASP doesn’t need to route access through a broker or proxy, so it doesn’t impact end users’ experiences in speed of access or network performance.
Second, unlike a proxy-based solution, CASP provides an additive layer of security to your architecture. They work well with existing network security appliances, like your firewall, by providing an additional level of security and control over information stored in cloud applications, that a firewall or gateway can’t provide alone. A proxy-based cloud access security broker (CASB) simply duplicates the functionality of a firewall and puts it between your users and the applications they need to do their jobs. As a result, the user experience is slowed down even further (hitting, effectively, two different firewalls) with minimal to no additional security benefits.
Finally, most popular cloud applications advise against using a proxy-based CASB. Notably, Google and Microsoft have both published recommendations against their use. The main reason is due to a CASB’s inability to stay updated as they make upgrades to their application infrastructures; application developers make changes to protocols, authentication methods, and more fairly regularly.
Due to the nature of the CASB architecture, these changes can easily break the connection in any number of ways. Application developers (especially big ones like Google and Microsoft) do not commit to warning CASB developers when a change could impact their product. Nor will they slow down the development of their own products for the sake of CASB vendors. So when these updates happen, the CASB developers won’t know about it and they won’t realize the full extent of the impact and gaps it creates in your security infrastructure until those gaps are patched by the CASB developers.
It’s worth noting that some cloud security providers use Chrome browser extensions, rather than an agent or broker, to secure cloud access. They call it “agentless” cloud security, but an extension is simply a different type of proxy. Traffic is still directed through it, and they suffer from the same pitfalls as other CASBs. Furthermore, Google is planning a major overhaul of Chrome extension support that could throw the whole technology through a loop.
Cloud application security platforms, on the other hand, work as a nearly native feature within each cloud application. They develop deep one-to-one integrations using the cloud applications APIs (often in close partnership with the application provider). Only changes in API protocols can impact the effectiveness of a CASP, and those changes are continuously documented and updated for developers.
[SEE IT IN ACTION] Watch A Pre-Recorded API Cloud Security Demonstration On-Demand >>
APIs Play A Much-Needed Role in Cloud Security
Something else we learned from the 2018 Cybersecurity Insider Report is 35% of IT security professionals don’t think they are capable of keeping pace with SaaS application changes.
The good news is CTOs, CTsO, and CISOs can leverage API-based cloud application security platforms to roll with the punches without skipping a beat. These sophisticated platforms can also easily detect existing and/or new risks in cloud applications based on changes in OAuth permissions settings, customer complaints, security reports, and so much more.
Who’s In Charge Of Cloud Application Security, Really?
The shortest answer is the SaaS vendor and the customer (you!). But contrary to popular belief, the application vendor does not take responsibility for the security of your data through it’s services.
The SaaS vendor is responsible for securing the application’s infrastructure, as well as its APIs. This means that they are responsible for the security of the servers, networks, and code that makes the application a product for customers.
You are accountable for setting everything up the right way and making sure it’s all configured correctly. You’re also in charge of establishing and maintaining a zero trust security program. It’s also your job to monitor access to your cloud environment and control it with data loss prevention policies, phishing and malware protections, and so on.
For example, if a hacker hijacks one of your user accounts and starts to download sensitive information, send phishing emails to other users, etc. it’s your responsibility to detect and remediate that activity. Your SaaS provider is not responsible or accountable for the data that is exposed or any of the damages a breach incident may cause.
Cloud security is a top risk factor that IT managers cite as a major barrier to cloud transformation. But, for the vast majority of organizations and industries, the benefits far outweigh the risks. There are many facets to building an effective cloud computing security infrastructure, and securing the data created, stored, and accessed in company cloud applications is a big part of that.
What often ends up being lost in the cloud computing story is just how secure cloud computing actually is compared to on-premise. When an organization transitions to the cloud, it is outsourcing some of the more difficult infrastructure and server security operations to another vendor (often, to a vendor with a much larger and better funded security team such as in the case of Google and Microsoft).
Cloud computing is still relatively new, and the security risks are largely misunderstood. If your organization is using cloud applications, or you are planning a transition to the cloud, you need to understand what is required to properly secure it. You will also need to access the visibility and control, over access and use, that you had with on-premise software.

