Districts using Google Workspace and/or Microsoft 365 need new types of data loss prevention methods to secure sensitive information
No two data loss prevention tools are made exactly the same. When it comes to securing your school district’s data, you need the best-fit solution for your specific needs.
Think about it: You wouldn’t shovel snow with a rake, just like you wouldn’t rake leaves with a shovel. Both tools are made differently because they serve different purposes. Simply put, the same principle applies when you’re talking about data loss prevention (DLP).
With so many different DLP tools available, it’s important to understand how each one fits into your existing infrastructure before making a commitment. To give you the confidence that your chosen solution is best for your district, let’s dive into what each one has to offer.
Understanding your need for data loss prevention
By now you might be wondering: What is data loss prevention?
Generally speaking, data loss prevention refers to the set of technologies, processes, and best practices used to prevent sensitive information from leaving your district’s network, whether it be in a data breach or data leak. In other words, any and all data protection tools put in place that prevent personal data from falling into the wrong hands can be considered DLP technology.
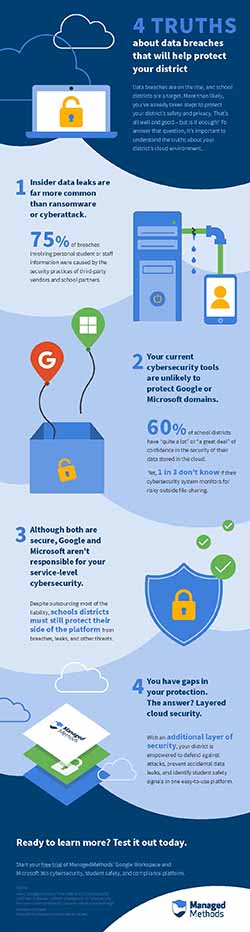
But do you really need data loss prevention in your district? The short answer is a resounding yes. In 2019, Edtech Magazine ranked education the least secure of 17 industries studied. According to our research in collaboration with EdWeek Research Center, little progress has been made in the years since. As a matter of fact, 50% of surveyed school districts either don’t know if their cloud security platform exists or they lack one entirely.
As if that’s not concerning enough, there are more threats to student data than ever before:
- Internal threats: Many factors inside your district could lead to accidental data leakage. From risky third-party applications installed on student devices to mistakenly attaching files to an external email – not to mention the threat of malicious insiders – there’s always a chance that data could be leaked.
- External threats: Across the ocean that is the internet, there’s plenty of pirates trying to toss your data overboard. Whether it be through malware, ransomware, or a phishing attack, cybercriminals are becoming increasingly sophisticated in their methods. In fact, data breach reports have risen year-over-year since 2016, per K12 SIX.
What does this mean for your district? Your sensitive data is at risk. With the proper data loss prevention tools in place, you have a much stronger chance of keeping it safe.
![[FREE RECORDING] How To Protect Student Data Privacy & Security in EdTech. WATCH HERE (no forms!)>>](https://no-cache.hubspot.com/cta/default/6834707/0d3d9aca-b6c5-448d-8883-c3a878631dd4.png)
Data loss prevention: Three key categories
Data loss prevention tools come in all shapes and sizes. That being said, not every DLP tool will fit perfectly in every part of your data security infrastructure.
To piece this puzzle together, it’s best that you know how each type of DLP tool works, why they’re needed, and how they support your data loss protection effort.
1. Endpoint DLP software
When you think about how students and teachers access sensitive information, you think about hardware. That’s where endpoint DLP comes into play. An endpoint DLP tool – sometimes called an endpoint protector – monitors data as it moves between smartphones, tablets, and computers.
By doing so, this can help your security team track how students and teachers are accessing, storing, and sharing personal data between one another. In turn, you can reduce the risk of an accidental data leak.
All in all, endpoint data loss prevention software offers greater device control, but only on devices where the DLP software is installed. For this reason, it’s best to complement your endpoint protection with network and cloud DLP technology.
2. Network DLP tools
On the other hand, network security focuses on protecting sensitive information by placing a secure perimeter around your data in motion. Rather than only monitoring data at the endpoints, network DLP keeps a watchful eye over personal data as it moves in and out of your school network.
A proper network DLP solution can automatically encrypt, block, quarantine, and audit the content of an email, document or other communication that may contain sensitive information. Likewise, administrators can remove access rights to certain files as they assess the situation. With the enhanced visibility that network security provides, your security team can easily prevent data leakage and reduce the risk of an outside data breach.
While an endpoint protector safeguards data as it’s used on each device, network DLP secures the perimeter with constant surveillance so that nothing malicious or dangerous goes in or out. Although effective together, there still remains a massive vulnerability: Data stored in the cloud.
3. Cloud security
Cloud DLP patrols the sky – no pun intended. With more than 90% of K-12 schools operating in the cloud, it’s never been more important to close the final gap in data security. In essence, this type of integrated DLP tool focuses on protecting learning technologies and services that use cloud storage.
Whether it be Google Workspace or Microsoft Office 365, cloud-based applications are storing plenty of personal data. Because they store information in the cloud, network firewalls and secure gateways do little to protect your data.
Through cloud monitoring, your district can receive real-time notifications when data has been improperly accessed, shared or saved from the cloud. Better yet, cloud DLP will automatically scan the content of shared files for personally identifiable information and other indications of sensitive data, allowing you to step into action in a moment’s notice.
Why your sensitive data is best protected by the cloud
It’s important to remember that data stored in the cloud is fundamentally different from data stored elsewhere. Because cloud data isn’t stored on an on-premise hard drive or local server, it’s therefore stored outside of your network – hence why perimeter network security can’t protect it.
Given the necessity for remote learning and hybrid work in recent years, it’s no wonder that schools and businesses alike have accelerated their leap to the cloud. But in the process of that expedited migration, critical cloud security measures are being missed.
This is a major problem, and here’s why: research shows that 83% of organizations are failing to encrypt their cloud data, while 40% have experienced a cloud data breach in the past 12 months. In other words, limited security controls are leaving sensitive data up for grabs where anyone might access it.
Benefits of cloud DLP tools
When it comes to protecting student information stored in your cloud environment, you need a DLP software that packs a punch. Empowered by a cloud-based data loss prevention solution, you stand to gain plenty of key advantages:
- Integrated DLP: Cloud solutions can easily integrate with SaaS products, including Google Workspace and Microsoft 365. With near-native security, you can protect data in a frictionless experience.
- Data auditing: You can review historical data and classify it by risk, sensitivity, or any other criteria.
- Data classification: Data can automatically be scanned and classified as it’s created or uploaded into your cloud environment.
- 24/7 monitoring: Even if your security team is taking a break, your cloud DLP is still working, protecting data and enforcing your DLP policy.
- Automated DLP policy enforcement: When a policy violation occurs, your DLP software will automatically mitigate the risk in the most appropriate way.
![[FREE RECORDING] How To Protect Student Data Privacy & Security in EdTech. WATCH HERE (no forms!)>>](https://no-cache.hubspot.com/cta/default/6834707/0d3d9aca-b6c5-448d-8883-c3a878631dd4.png)
Understanding API vs. proxy-based cloud security
Let’s dive a little deeper and take a look at the two types of cloud data loss prevention tools: API and proxy-based solutions.
1. Proxy-based solutions
Proxy-based cloud DLP solutions use a proxy – a system that breaks the connection between sender and receiver – as a gateway that monitors users as they access data in the cloud. In basic terms, a proxy checks and filters known users and devices through a single gateway, allowing the software to take real-time action when risks are identified.
However, proxies cause significant delays in network performance. Think about it: Filtering all of your student data through a single gateway is like directing traffic into a single four-way intersection. Worse yet, proxies only check for known users, meaning unknown (or outside) threats may go undetected.
At its most simple, proxy-based cloud DLP tries to use network-level perimeter security to solve cloud-level challenges. Luckily, there’s a better way.
2. API-based solutions
API-based security doesn’t have any negative impact on network performance. Rather than use network technology, these solutions are built on a cloud application’s native Application Programming Interface (API). An API is simply a set of definitions and protocols that allow you to build and integrate application software, such as a DLP solution.
What does this mean for you? Because API-based solutions are integrated into your cloud services, they secure both known and unknown users. As a result, you gain direct, secure access to the cloud from any device. As a near-native part of the application, API-based DLP are far more effective at monitoring data activity within the app itself.
Best of all, APIs are built on an open architecture, which means that your security team can customize access rights, rules, and policies to your choosing. Plus, they’re ready-to-go with out-of-the-box data loss prevention capabilities for rapid deployment.
Whereas proxy-based solutions duplicate network functionality, API-based DLP provides an additional layer of security.
Everything you need in your data loss prevention toolbox
Protecting student privacy comes down to how effectively you use your data loss prevention tools. Of course, the quality of those tools will make that challenge easier on you and your district.
Be sure your choice is fully equipped with the following critical features and capabilities:
- Out-of-the-box DLP policies: Who’s to say the needs of your school district are exactly the same as anyone else’s? Customizable rules allow you to determine how each DLP policy is enforced by your cloud solution. Better yet, pre-built policies save you time and kickstart your data loss protection effort while you build new ones as you see fit.
- Content scanning: Content-aware artificial intelligence scans for key terms, phrases, text strings, and numbers based on your predetermined DLP policy. In other words, if students or staff are sharing personally identifiable information, your DLP software will identify it quickly and begin remediation. Most importantly, you can also identify signals of self-harm, cyberbullying, threatening, and explicit content that could indicate a danger to student safety.
- Machine learning capabilities: While the students are learning, your DLP solution is, too. Machine learning allows your software to become more effective and efficient over time, thus reducing false positives by a significant margin. The software, in turn, will grow to recognize complex data loss threats as time goes on.
- Unauthorized app discovery: If a student or staff member installs an unsanctioned third-party app or browser extension to a device, your DLP tool can identify this action right away. Moreover, it’ll perform a risk assessment of that app and respond accordingly.
- Real-time alerts: When your cloud solution identifies a DLP policy violation, it’ll send instant administrator alerts and user notifications. Not only does this give the user context as to what happened to their communication, but it also allows administrators to investigate as quickly as possible.
- Enhanced control: Greater visibility into your cloud environment allows you to control how files are downloaded, printed, or copied from your applications. In turn, you’re able to revoke access rights, change permissions, and disable certain actions.
- Automated remediation: The fact of the matter is that DLP policy enforcement is a lot of work – that’s what automation is for. The best DLP solutions can automatically take action when a violation occurs, allowing administrators to focus their efforts elsewhere. The software can even delete, unshare, and quarantine files based on your policy settings.
- Phishing and malware protection: To reduce the risk of cybercrime, DLP tools can automatically scan the body and attachments of emails for possible threats. Risky emails are then quarantined for review or deleted if the threat is confirmed.
These features, among many more, are vital assets in your data loss prevention toolbox. Without the additional layer of security that an API-based cloud DLP tool provides, your school district’s data is likely still at risk.
Now that so much of your data is stored in the cloud, it’s time to close the final gap in your security. At ManagedMethods, our out-of-the-box cloud security platform is fully equipped with automated capabilities, data monitoring features and customizable policies to match your complex data protection needs.
Learn more about how our data loss prevention tool can protect sensitive data in your district by requesting a 30-day free trial today.

