Google Workspace & Microsoft 365 data protection
Data Loss Prevention Software for School Districts
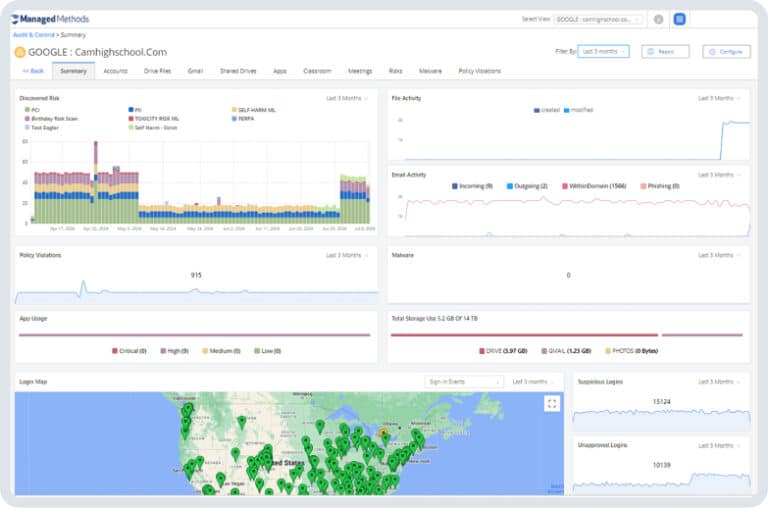
Our data loss prevention software helps K-12 schools protect sensitive data in Google Workspace and Microsoft 365, ensuring compliance and security against unauthorized access and accidental exposure.
Security for your data
Advanced cloud data loss prevention for real-time data protection
ManagedMethods’ cloud DLP software provides real-time monitoring and automated response to suspicious activities, ensuring that sensitive student, staff, and district information remains secure. Key features include identifying risky sharing settings, detecting anomalous behavior, blocking unauthorized data sharing, and providing detailed audit logs for compliance reporting. With our DLP software, schools can proactively address data security threats and maintain a safe digital environment.
How can cloud DLP software enhance data security?
AI-driven security monitoring
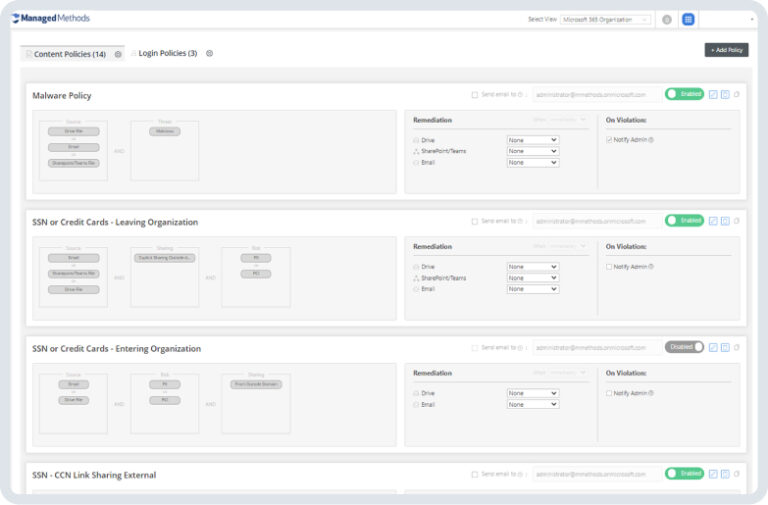
Cloud DLP leverages artificial intelligence and keyword scanning to automate data loss prevention, constantly monitoring and enforcing rules that dictate how data should be handled. Key aspects of cloud DLP include:
- DLP policy enforcement automates the application of rules governing how data can be accessed, shared, edited, or deleted.
- Image scanning employs optical character recognition to check for DLP policy violations in image files, such as pictures of credit cards.
- Third-party risk identification evaluates risks from third-party SaaS applications, mitigating threats by monitoring and eliminating risks from external sources.
Automated Remediation
When risks are detected, Cloud DLP swiftly acts to mitigate them, automating the management of threats until a detailed review can be conducted. Automated actions include:
- Revoke sharing privileges automatically if a user violates a DLP policy.
- Suspend accounts temporarily to restrict a user's access to documents pending further investigation.
- Quarantine content intercepts file sharingcontaining risky or sensitive information for detailed review.
- Revoke access granted to third-party apps connected to your data through OAuth.
Case study
Lenoir City Schools
“Give Cloud Monitor a try! I recommend it to other districts that are looking for this type of solution. The free audit is full-blown, so you’re truly able to demo the full product before you buy. And it’s absolutely worth it to help keep our kids safe.”
Wes Rhodes
Network Administrator, Lenoir City Schools
Use Cases
Discover more use cases
Student Self-Harm Detection
Ensure the security of sensitive information stored in your district’s Google Workspace and Microsoft 365.
Phishing & Malware Protection
Secure your district from phishing attacks and malware threats with proactive monitoring and threat detection.
Account Takeover Prevention
Protect against unauthorized access to user accounts with our account takeover prevention features.
Get in touch
Safeguard your district’s data with ManagedMethods
ManagedMethods provides easy-to-use data loss prevention software tailored for educational institutions. Request your free trial today and ensure comprehensive protection for your district's sensitive data in Google Workspace and Microsoft 365.