Sleep soundly knowing that your data is protected by these Google Cloud Platform security features
Many IT leaders and managers are still nervous about moving their districts to cloud computing, mainly citing cloud security concerns. However, Google Cloud Platform security features are among the best on the market, including traditional network security. It is important for IT security managers to know that a Google cloud infrastructure security breach is extremely rare. It’s also important to keep in mind that Google’s security team is among the best in the world.
The main thing that people tend to get wrong about Google cloud security issues is the difference between infrastructure security and Google Apps security. While Google retains responsibility for securing the infrastructure that Apps services, such as G Suite, are built on, it’s the customer’s responsibility to secure their own domain using that service.
Cloud computing offers school districts greater flexibility, collaboration, and productivity. Resisting the transition to the cloud could actually be doing more harm than good. Let’s take a deeper look into the layered security features available to Google Cloud customers.
[READ MORE] 5 Google Cloud Security Best Practices >>
Google Cloud Platform Security Infrastructure
The Google Cloud platform infrastructure uses multiple layers of security. Because redundancy is built into the progressive layers of security, no one incident can take down the Google Cloud infrastructure. Google Cloud security layers includes everything from physical security at data centers to some of the most advanced cybersecurity technology and professionals available in the world.
Google Cloud Platform Infrastructure Security Features Include:
- 24/7/365 operations, device security detection and response from both internal and external threats
- Data in-transit encrypted communication to and from Google’s public cloud, including layered defense redundancies to protect customers from denial-of-service (DoS) attacks
- Identity protection and management through multiple authentication factors
- Data at-rest storage security using encryption against unauthorized access and distribution for reliability
- An entire hardware infrastructure created, built, controlled, and secured by Google including servers, networking equipment, and security chips
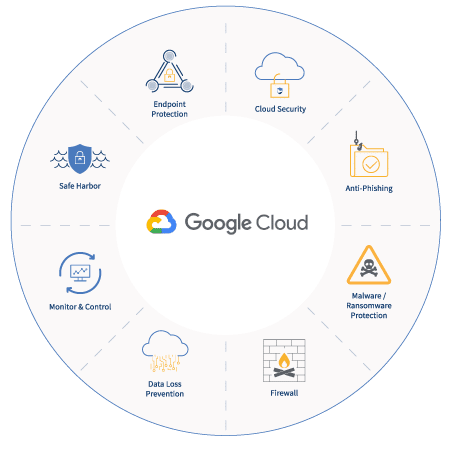
Google Cloud Platform Security Products
Google has not only built the most secure cloud platform available as a service, but also provides security products to customers. These security products help any type of organization secure operations and communication in the cloud. Some Google Cloud security products are provided through G Suite licenses, while others are purchased separately.
Google Cloud Platform Security Products Features Include:
- Infrastructure Security: Google’s “secure-by-design” infrastructure security product includes features such as hardening, configuration management, and vulnerability management for Google Cloud customers.
- Network Security: Google Cloud’s network security products include Virtual Private Cloud, Cloud Load Balancing, Encryption, and Application Layer Transport Security to help customers define, enforce, and secure their perimeter.
- Endpoint Security: The number of endpoints in districts has exploded over recent years! Google Cloud Platform can help secure endpoints with device management, patch and vulnerability management, and device hardening for Chromebooks, Chrome OS, Chrome Browser, and G Suite Device Management.
- Data Security: Google Cloud provides a wide range of data security features at different license levels to support discovery G Suite data loss prevention, data governance, and more.
- Identity & Access Management: Identity and Google Cloud access security features authentication and identity management in G Suite, system access management and more. Add-on Google Cloud security products include Cloud Identity, Cloud Identity-Aware Proxy, and Security Keys.
- Application Security: Google Cloud application security is a necessity for any school district storing sensitive student, faculty, staff, and/or financial information in Google Cloud (including G Suite applications such as Gmail, Drive, and Shared Drives).
{FREE WEBINAR} The State of K-12 Cybersecurity & Student Data Privacy. Learn More & Register >>
Google Cloud Platform Security Transparency & Privacy
Simply put, Google Cloud Platform is not going to Zuckerberg your business data. It is absolutely critical to their business model to keep your district’s data private and secure both in-transit through the Google Cloud network and at-rest in data servers.
Google is committed to keeping customers’ data private. The company has outlined its commitment to transparency, privacy, and trust by publishing six Google Cloud Trust Principles.
6 Google Cloud Security Trust Principles
- Your security comes first in everything we do. Google commits to promptly notifying system admins if a security breach is detected that may have compromised your data.
- Control what happens to your data. Google Cloud customers maintain total control of their data at all times; it can be accessed or removed at any time. Customer data is processed by Google in accordance with your instructions.
- Customer data is not used for advertising. It’s no secret that a big chunk of Google’s revenue is made in advertising. However, data stored in Google Cloud is completely separate from that business and is never used for advertising purposes.
- Know where Google stores your data and rely on it being available when you need it. Google’s data center locations are publicly available. They are distributed throughout the world to ensure against natural disasters and are protected by the most advanced security team on the planet.
- Google’s security practices are independently verified. Google Cloud security practices are audited, certified, and validated by independent auditors to ensure strict adherence to international security and privacy standards.
- Google will never give any government entity “backdoor” access to customer data. Google actively rejects invalid government requests for data and publishes a transparency report of government requests
Google Cloud Platform Security Partners
Google Cloud Platform security features are robust and constantly improving. Yet many customers decide they need to augment Google security features with third-party vendors. This could be for a variety of reasons, including security redundancy, cost, and ease of use. K-12 IT and student safety teams find using a G Suite cyber safety and security monitoring platform developed specifically for the unique needs of K-12 school districts particularly beneficial. Recognizing this, Google Cloud Platform now supports a significant Partner program to help customers find identity certified and verified Google cloud vendors.
The Google Cloud Platform (GCP) Partner Program doesn’t just include security vendors. It incorporates any type of product or service a customer may need to effectively use Google Cloud products. It includes resellers, services, technology, and training partners for every Google product. Partner network capabilities include application development, cloud migration, data analytics, IoT, security, and much more!

